The challenge of managing knowledge in cybersecurity
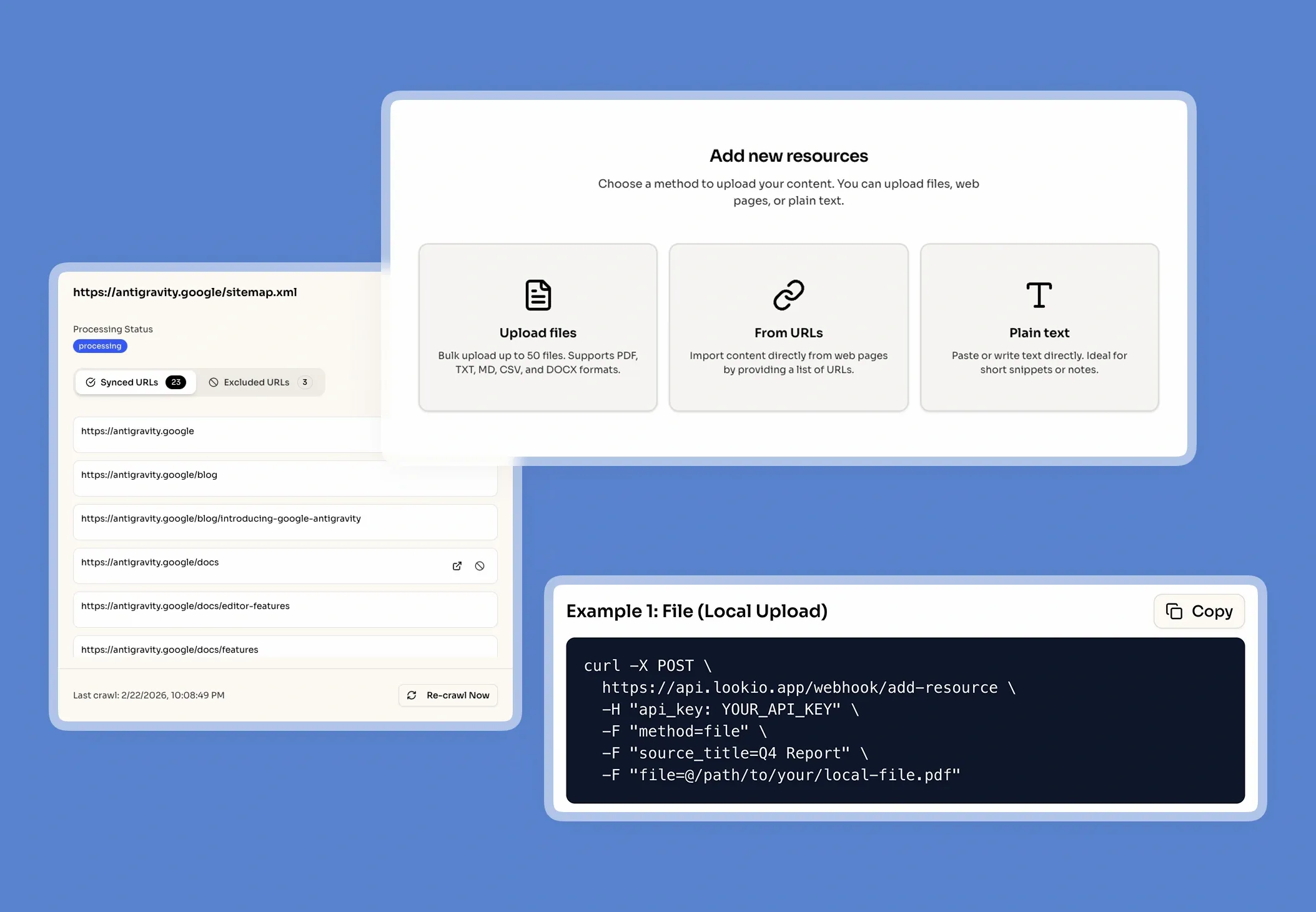
When a security researcher or incident responder tries to validate a threat against internal compliance frameworks, they hit a wall of unstructured data. Cybersecurity firms are sitting on thousands of pages of proprietary audit reports, specialized threat intelligence, and sensitive SOC procedures that are effectively locked away in silos.
The high cost of expert interruptions
In the high-stakes world of cybersecurity, information decay is rapid. What fails in the current workflow is the reliance on tribal knowledge. Senior analysts are constantly interrupted by junior staff to explain specific internal protocols or past incident resolutions. This doesn't just waste time; it creates a massive SLA risk during active breaches. Every minute spent digging through a SharePoint folder for the right hardening guide is a minute a threat actor has to move laterally through a network.
Why the tools they've tried fall short
Most firms have already attempted to solve this with standard internal tools, but the results are consistently disappointing:
- Internal wikis and keyword search: Basic keyword matching fails when an analyst searches for "lateral movement patterns" but the documentation uses specific technical jargon like "pass-the-ticket escalation." You need semantic understanding, not just a search bar.
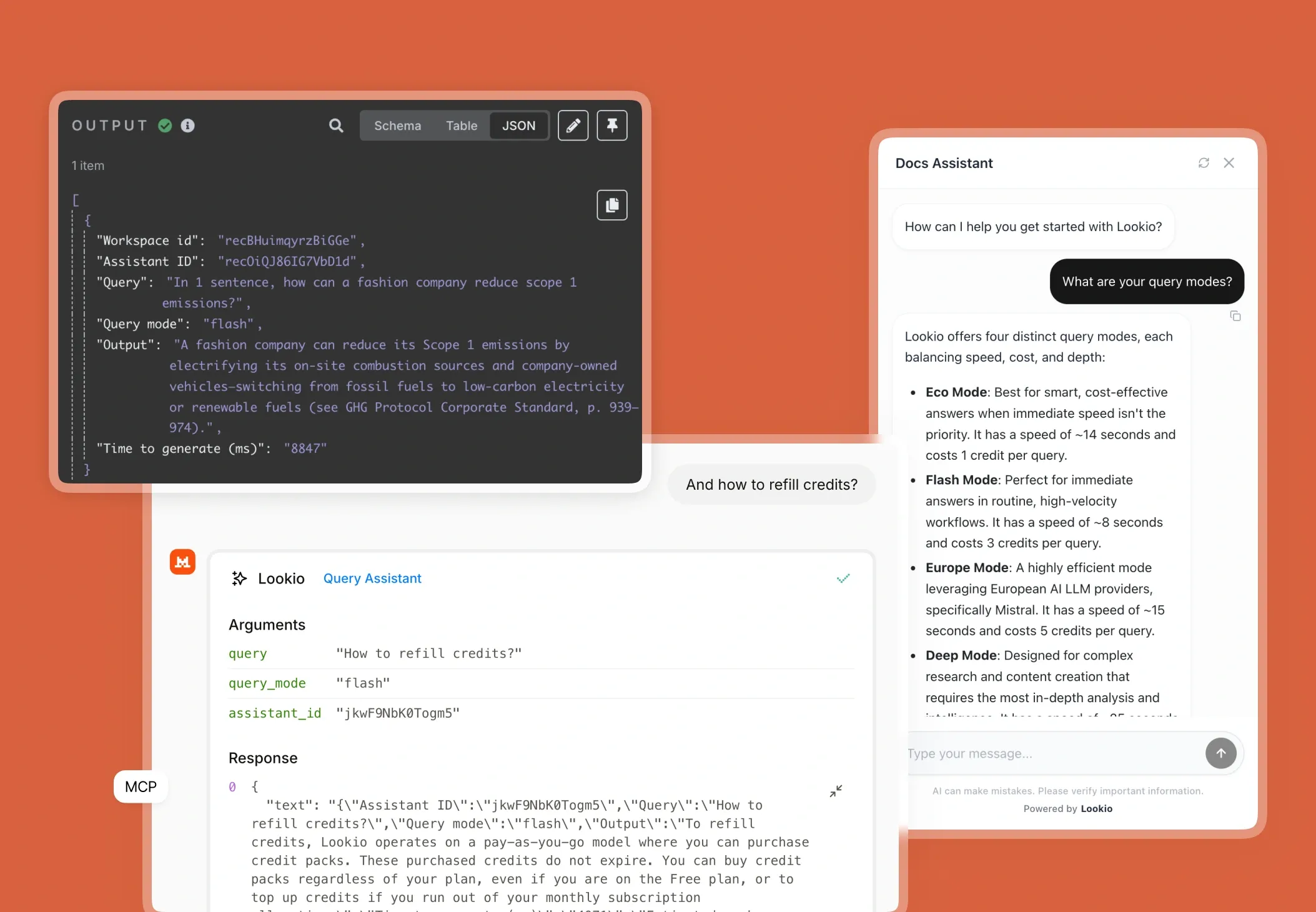
- Generic AI (ChatGPT/LLMs): While fast, generic models are a significant security risk and frequently hallucinate on technical specifics. Asking a generic LLM to summarize a custom firmware audit can lead to dangerously inaccurate security recommendations because it lacks the context of your private files.
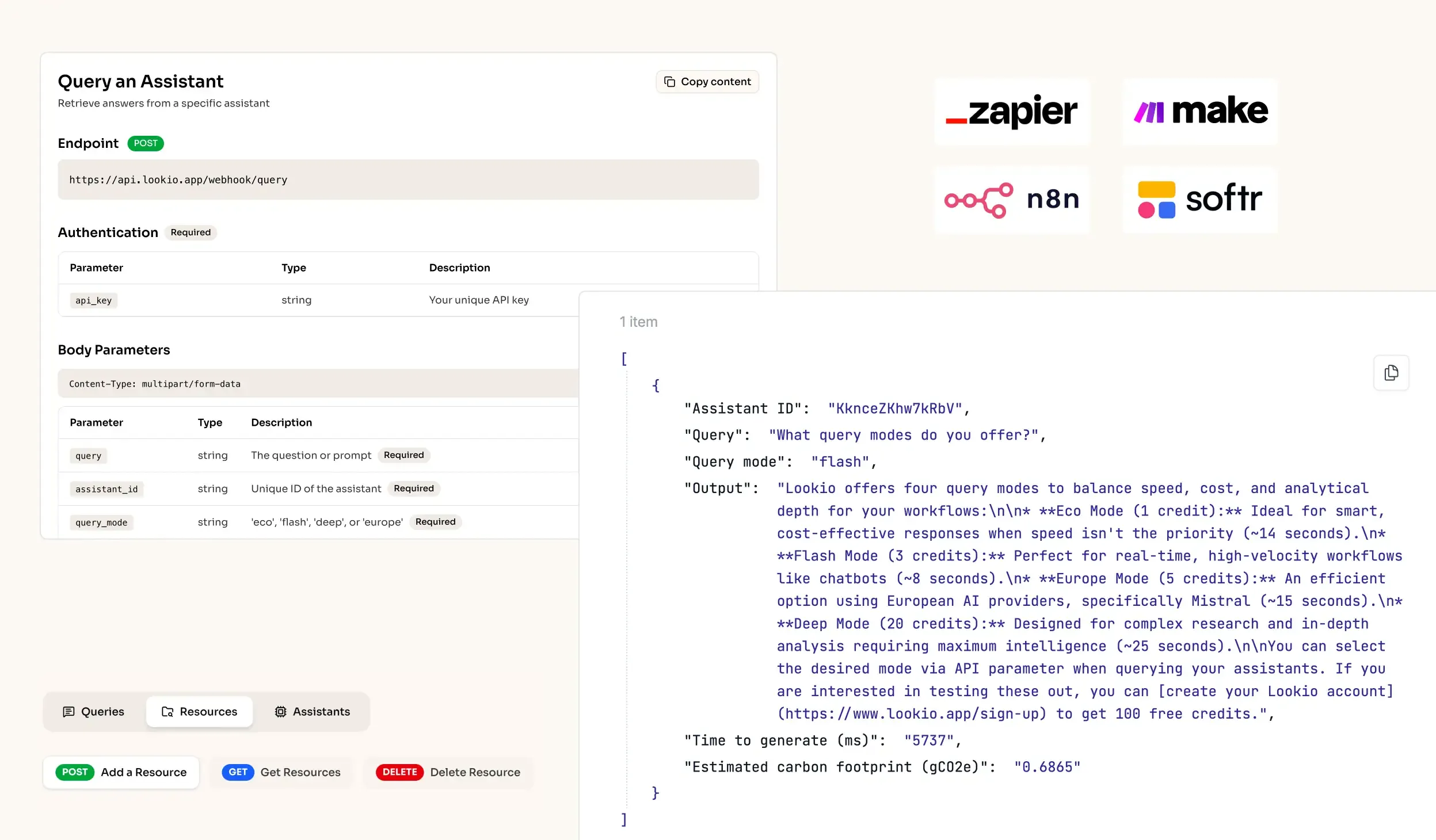
- No-API tools like NotebookLM: While great for individual research, tools like NotebookLM lack an API, making it impossible to trigger knowledge retrieval from within an automated SOC or a ticketing system.
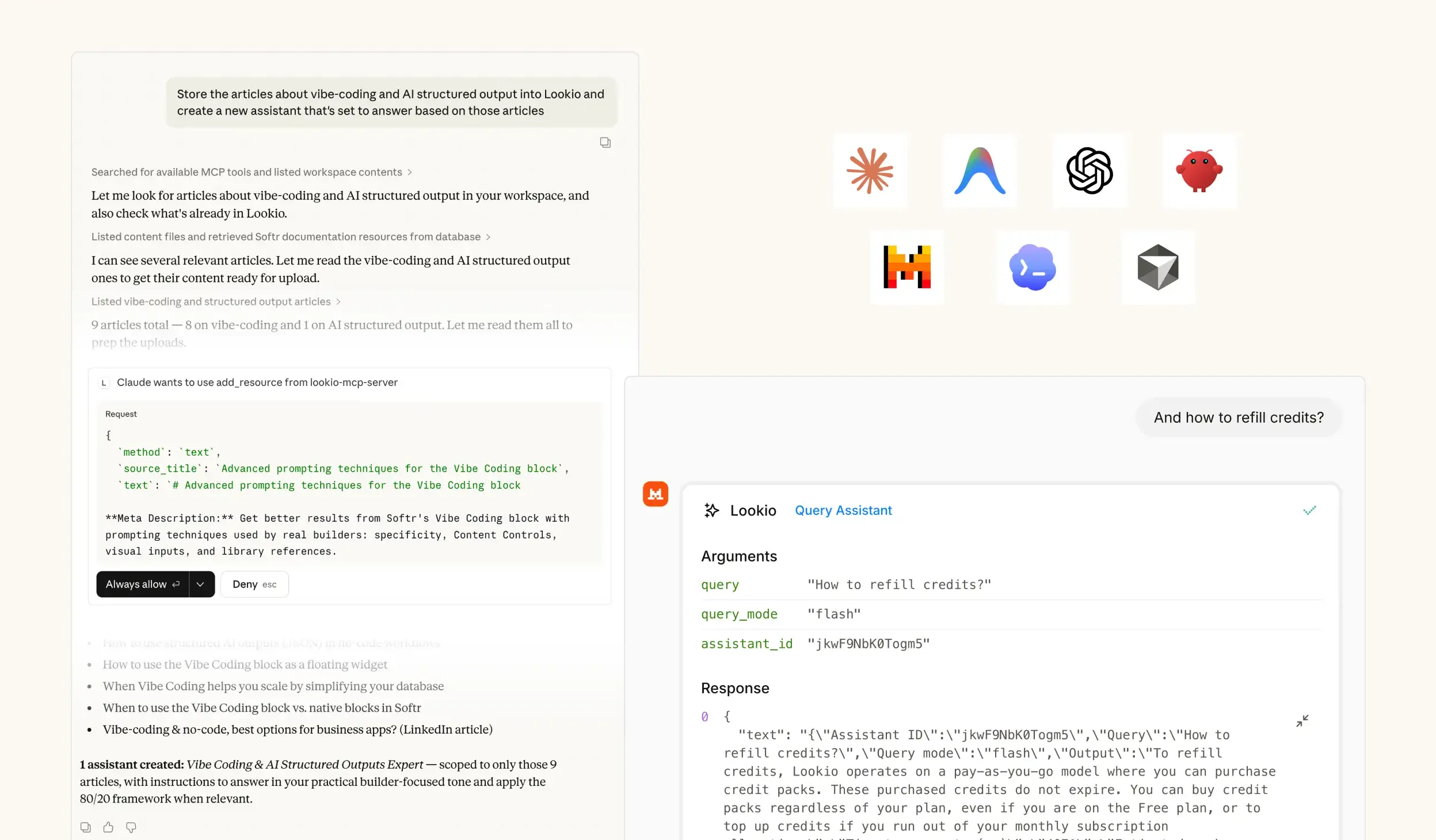
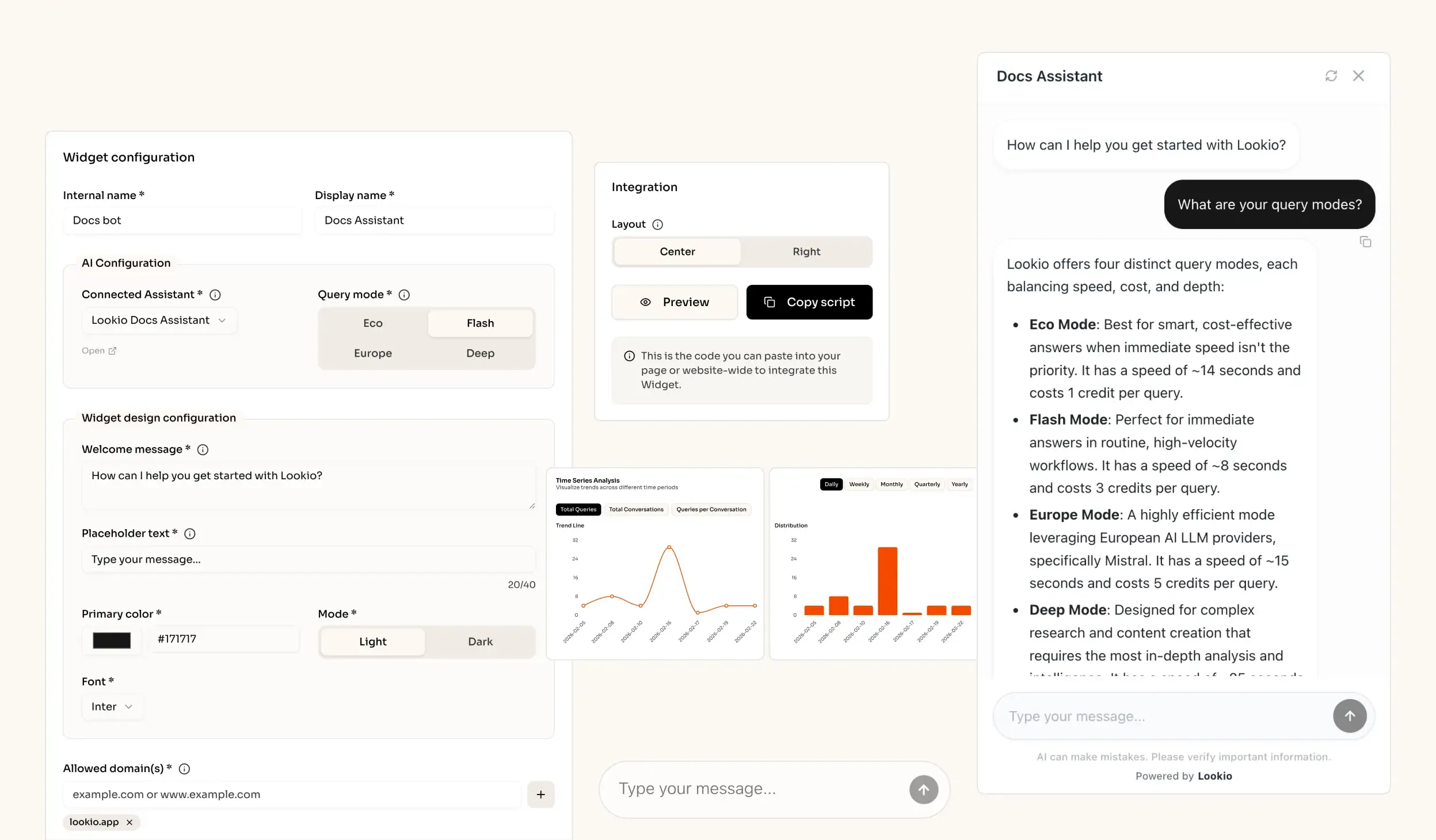
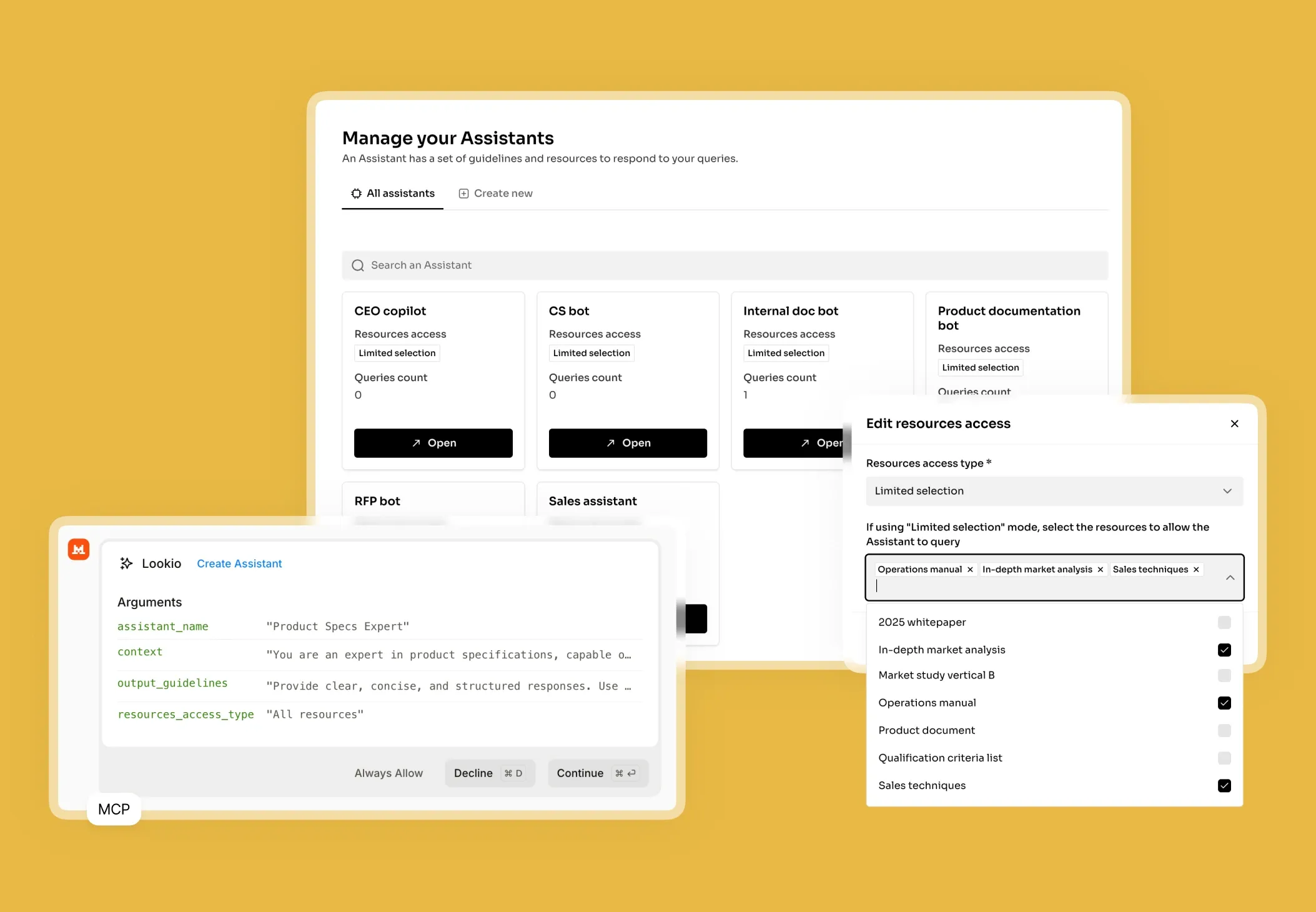
What's missing is a way to bridge the gap between your secure documentation and the frontline analysts who need those insights programmatically and instantly.